Our Services
Licensed Private Investigation, Security & Digital Forensics Services in the Detroit Metro Area, MI
Metro Detective Agency delivers licensed, court-ready investigative and protective services from our Livonia, MI headquarters to clients across Michigan. We combine traditional investigative tradecraft, disciplined field operations, and advanced cyber forensics to deliver verifiable evidence and practical recommendations tailored to legal, corporate, insurance, and private client needs.
Ready to discuss your case?
248-315-2440 – Office – 24/7

Personal Protection & Executive Security Services

Personal Escort & Protective Services (Armed and Licensed)
Our agency provides discreet, highly trained, armed, and licensed protective personnel for clients who require enhanced personal security. We offer secure escort services for individuals, executives, high-profile clients, and at-risk persons during travel, public appearances, private events, and everyday movement. Our protection specialists are carefully vetted and professionally trained in defensive tactics, situational awareness, threat assessment, emergency response, and conflict de-escalation. We develop and implement comprehensive protection strategies that include advance planning, route analysis, venue security sweeps, and coordination with local law enforcement or event staff when appropriate.
We maintain strict confidentiality, operate with the utmost professionalism, and tailor every protection plan to the client’s specific risk level, environment, schedule, and personal preferences. Our teams are equipped to provide both overt and discreet protective postures, adaptive threat mitigation, secure transportation, and rapid evacuation protocols. We also offer pre-engagement consultations, ongoing risk monitoring, and post-event debriefings to ensure continuous improvement and client peace of mind.
Security Consulting
We offer comprehensive security assessments and consulting services designed to identify operational vulnerabilities and recommend practical, actionable mitigations. Our assessments encompass a full range of physical and procedural reviews, including perimeter and access-control evaluations, CCTV and alarm system audits, facility hardening recommendations, and emergency power and redundancy checks.
We conduct insider risk analysis that combines personnel vetting, behavioral indicators, access-pattern reviews, and policy audits to detect and reduce the threat posed by trusted insiders. Our incident response planning services produce clear, scalable playbooks for a variety of scenarios—cyber-physical incidents, active threats, workplace violence, data breaches, and business continuity events—and include roles and responsibilities matrices, communication protocols, and tabletop exercises to validate readiness.
We provide executive security advisories tailored to corporate needs, covering personal protection for senior leaders, secure travel guidance, residential security recommendations, and executive-specific policy development. Our consulting engagements also include security governance reviews, vendor and third-party risk assessments, training programs for staff and security teams, and prioritized remediation roadmaps that align with your business objectives and budget. Each engagement concludes with a detailed report, risk-ranked recommendations, and a practical implementation plan to improve resilience and reduce exposure.

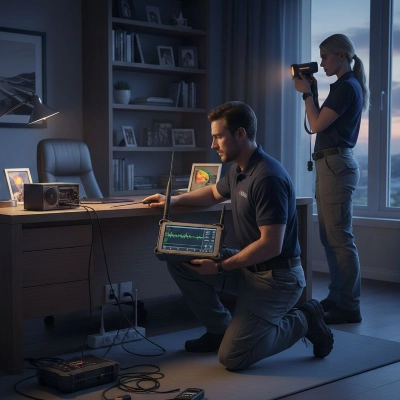
Bug Sweep Services (Technical Surveillance Countermeasures)
Technical sweep services identify and locate active or dormant audio/video surveillance devices, unauthorized transmitters, and hidden cameras to protect privacy, intellectual property, and corporate confidentiality. Our technicians perform discreet, methodical sweeps of offices, conference rooms, executive suites, hotel rooms, vehicles, warehouses, and other sensitive spaces, tailoring scope and intensity to client concerns and threat profiles.
We employ a layered detection approach that combines RF detection and spectrum analysis to find transmitting devices, non‑linear junction detectors (NLJDs) to reveal electronic components (even when not powered), thermal imaging and low‑light optical inspection for lens detection, and physical inspection protocols to uncover concealment points in furniture, fixtures, lighting, and structural elements. Technicians also examine wired infrastructure, power supplies, and network endpoints for covert recording devices, inspect IoT devices and consumer electronics for unauthorized functions, and review Bluetooth and Wi‑Fi environments for suspicious endpoints and data exfiltration channels.
Our tools include calibrated RF scanners, broadband and directional antennas, spectrum analyzers, NLJDs, endoscopes and borescopes, thermal cameras, magnetometers, and portable network analyzers, supported by practiced manual search techniques and checklists to ensure thorough coverage. Sweep procedures follow documented methodologies: perimeter scans, zone sweeps, static sweeps of fixed points, and dynamic sweeps during staged activities to detect intermittent or motion‑activated devices. For high‑risk environments we integrate layered timing sweeps and follow‑up inspections to capture devices that cycle or are remotely activated.
When suspicious items are identified, we document findings with time‑stamped photographs, audio recordings (where lawful), device metadata capture, and detailed technical notes. If removal or seizure is requested, technicians follow chain‑of‑custody and evidence‑preservation protocols and coordinate with legal counsel or security teams to manage escalation. We also produce comprehensive technical reports that describe detection methods, instruments used, findings, risk assessments, and recommended remediation actions—such as device removal, physical hardening, electronic countermeasures, network segmentation, or policy and training updates.
Post‑sweep services include remediation support (device removal and secure disposal), recommendations for counter‑surveillance design (secure room layouts, shielding, and tamper‑resistant fixtures), follow‑up monitoring plans, and periodic sweep schedules to maintain protection over time. For corporate clients we can integrate technical sweeps into broader security programs, provide executive‑suite protection certifications prior to high‑level meetings, and offer briefings for in‑house security or IT teams.
All sweep activities are conducted in accordance with applicable laws and client authorizations, with strict confidentiality and secure handling of any discovered materials. Our priority is to deliver clear, actionable detection and mitigation outcomes that reduce exposure, restore confidence in sensitive environments, and support compliance with privacy and corporate‑security obligations.
Corporate, Fraud & Claims Investigations
Corporate Fraud / Claims Investigations
We provide comprehensive pre‑transaction and vendor due‑diligence services to assess risk, reputation, and regulatory compliance across mergers and acquisitions, strategic partnerships, joint ventures, and vendor onboarding. Our tailored diligence engagements are scoped to transaction size, geographic footprint, industry sensitivities, and the client’s specific risk appetite, delivering actionable intelligence that supports deal decisions, informs negotiation strategy, and mitigates post‑closing surprises.
Core services include multi‑jurisdictional public‑record searches, corporate and registry filings review, and beneficial‑ownership and corporate‑structure mapping to reveal hidden stakeholders, nominee arrangements, and ultimate economic beneficiaries. We perform adverse‑media screening, sanctions and watch‑list checks, politically exposed person (PEP) screening, and litigation and judgment searches to surface reputational, legal, and regulatory red flags. Financial background checks and basic financial‑profile analysis—bankruptcies, liens, tax judgments, creditor actions, and material encumbrances—are integrated where relevant to evaluate counterpart solvency, contingent exposure, and potential impact on transaction value.
Enhanced due diligence options examine operational standing and integrity through onsite verification and facility inspections, management and owner interviews, vendor and supplier reference checks, site photographs, and validation of licenses, certifications, permits, and compliance programs. For complex or cross‑border matters we add targeted forensic accounting reviews, transaction‑trail analysis, AML/KYC posture assessments, and screening for fraud indicators, related‑party transactions, or concealed revenue streams that could affect valuation or create post‑closing liability.
We also conduct supply‑chain and third‑party risk reviews to identify concentration risks, subcontractor vulnerabilities, and sanctions‑exposure pathways; intellectual‑property and regulatory‑compliance scans to detect registration gaps, enforcement histories, or infringement claims; and cyber posture overviews that flag public incidents, unresolved breaches, or systemic weaknesses that could translate into integration or operational risk. Environmental, social, and governance (ESG) screening and sector‑specific regulatory checks are available for industries with heightened compliance obligations.
Deliverables are concise, decision‑focused reports that include executive summaries, risk‑ranked findings, source‑referenced evidence, ownership charts, flow diagrams of related entities, adverse‑media dossiers, and recommended mitigations—such as contractual protective clauses, escrow or holdback structures, enhanced warranties, indemnities, or conditional approval thresholds. Where appropriate, we prepare memoranda suitable for inclusion in due‑diligence data rooms or board materials and provide briefing sessions and Q&A to help deal teams interpret findings, quantify risk, and prioritize follow‑up actions.
Throughout engagements we apply rigorous source validation, document and citation practices, and secure handling of sensitive data with encrypted communications and restricted access. We coordinate with legal, tax, financial‑advisory, and compliance teams to align scope with regulatory obligations and to enable seamless integration of investigative findings into transaction documentation and negotiation tactics. Expedited, phased, and ongoing monitoring services are available to update risk profiles through the deal period and into post‑closing integration, providing watchlist alerts, re‑screening of counterparties, and change‑in‑circumstance reporting to help clients close with greater confidence and reduce downstream surprises.

Due Diligence
We provide comprehensive pre‑transaction and vendor due‑diligence services to assess risk, reputation, and regulatory compliance across mergers and acquisitions, strategic partnerships, joint ventures, and vendor onboarding. Our tailored diligence engagements are scoped to transaction size, geographic footprint, industry sensitivities, and the client’s specific risk appetite, delivering actionable intelligence that supports deal decisions and mitigates post‑closing surprises.
Core services include multi‑jurisdictional public‑record searches, corporate and registry filings review, and beneficial‑ownership and corporate‑structure mapping to reveal hidden stakeholders, nominee arrangements, and ultimate economic beneficiaries. We perform adverse‑media screening, sanctions and watch‑list checks, politically exposed person (PEP) screening, and litigation and judgment searches to surface reputational, legal, and regulatory red flags. Financial background checks and basic financial-profile analysis—bankruptcies, liens, tax judgments, and creditor actions—are integrated where relevant to evaluate counterpart solvency and contingent exposure.
Enhanced due diligence options examine operational standing and integrity: onsite verification and facility inspections, management and owner interviews, vendor and supplier reference checks, site photographs, and validation of licenses, certifications, and permits. For complex or cross‑border matters we add targeted forensic accounting reviews, transaction‑trail analysis, AML/KYC posture assessments, and screening for fraud indicators or related‑party transactions that could affect valuation or post‑deal liability.
We also conduct supply‑chain and third‑party risk reviews to identify concentration risks, subcontractor vulnerabilities, and sanctions‑exposure pathways; intellectual‑property and regulatory‑compliance scans to detect registration gaps or enforcement histories; and cyber posture overviews that flag public incidents or systemic weaknesses that could translate into integration risk.
Deliverables are concise, decision‑focused reports that include executive summaries, risk‑ranked findings, source‑referenced evidence, ownership charts, adverse‑media dossiers, and recommended mitigations—such as contractual protective clauses, escrow or holdback structures, enhanced warranties, or conditional approval thresholds. Where appropriate, we prepare memoranda suitable for inclusion in due‑diligence data rooms or board materials and provide briefing sessions to help deal teams interpret findings and prioritize follow‑up.
Throughout engagements we apply rigorous source validation, document and citation practices, and secure handling of sensitive data. We coordinate with legal, tax, financial‑advisory, and compliance teams to align scope with legal obligations and to enable seamless integration of investigative findings into transaction documentation. Expedited and ongoing monitoring services are available to update risk profiles through the deal period and into post‑closing integration, helping clients close with greater confidence and reduce downstream surprises.
Insurance Fraud / Claims Investigations
Our claims and subrogation investigations detect staged losses, fraudulent injury claims, and policy abuse using a systematic, evidence‑based approach designed to protect insurers, reinsurers, self‑insured entities, and corporate risk managers. We combine investigative disciplines—covert and overt surveillance, targeted witness interviews, scene and vehicle inspections, records acquisition and analysis, and technical forensics—to validate or refute claim details and quantify potential recoverable exposures.
Investigative activities include advance case scoping and liaison with claims examiners to define hypotheses and thresholds for investigative escalation. Field operations may employ covert surveillance to document claimant activity patterns, mobility, and inconsistencies with reported injuries; site and vehicle examinations to identify staging indicators; and on‑scene measurements and photographic documentation to corroborate or challenge loss narratives. We conduct comprehensive records reviews—medical records and billing audits, employment and wage verifications, repair and maintenance histories, prior claims analysis, and insurance policy examinations—to detect anomalies, billing irregularities, or undisclosed preexisting conditions.
We perform witness interviews and statements following legal and evidentiary best practices to preserve credibility, and we coordinate with medical experts, biomechanics specialists, and vocational evaluators when injury causation or impairment is contested. Forensic services may include video and image analysis, telematics and GPS data review, digital device forensics, and laboratory testing of materials or damage patterns. Where financial recovery is possible, our subrogation work traces third‑party liability, documents compensable loss elements, and supports demand letters, settlement negotiations, or civil recovery actions.
Deliverables are tailored to claims workflows and litigation needs: concise investigative reports, time‑stamped multimedia exhibits, authenticated transcripts and affidavits, chain‑of‑custody documentation, and quantified loss analyses ready for legal review. We also provide expert summaries and testimony support when cases proceed to arbitration or trial. Throughout engagements we coordinate with counsel and claims counsel to align methods with legal strategy, privacy obligations, and regulatory requirements.
Our protocols emphasize legal compliance, ethical standards, and claimant safety; investigators are trained to minimize confrontation and to document encounters for defensibility. Evidence handling follows strict chain‑of‑custody and secure storage practices, and we maintain detailed case logs and source citations to support adverse‑action decisions or recovery initiatives. By integrating meticulous fieldwork, technical forensics, and financial analysis, we help clients reduce fraud losses, strengthen recoveries, and improve overall claims integrity.

Employment Background Check Services
We provide customized background screening packages tailored for employment screening, executive vetting, vendor due diligence, and sensitive personal inquiries. Our offerings are modular and scalable so clients can select the combination of checks that best fits risk tolerance, regulatory obligations, and the role or relationship under review.
Searches combine comprehensive public‑record retrieval, proprietary commercial databases, and targeted manual verification to ensure accuracy, context, and defensibility. Core components include identity verification, multi‑jurisdictional criminal‑record searches, national and international watch‑list screening, civil‑litigation and judgment searches, bankruptcy and asset checks, motor‑vehicle records, and employment and education verification. For executive and high‑risk roles we add enhanced due diligence such as global adverse‑media screening, sanctions and politically exposed person (PEP) checks, corporate affiliation and beneficial‑ownership mapping, and asset and litigation history reviews.
We perform professional reference interviews, license and credential confirmations, social‑media and online footprint analysis, and address and residency history reconciliation. All adverse or potentially disqualifying findings are corroborated through secondary sources and, when appropriate, escalated to manual review by experienced investigators to reduce false positives and provide meaningful context.
Our process emphasizes compliance with applicable employment and privacy laws—including FCRA requirements in the U.S. where relevant—and we produce clear, well‑documented reports that distinguish verified facts from unverified leads. Deliverables can be formatted for HR systems or legal review and include summary risk ratings, source citations, copies of key records, and recommended follow‑up actions or interview lines.
We maintain secure data handling, encrypted communications, and strict access controls to protect candidate and client confidentiality. Turnaround times are aligned to client needs, with expedited options for urgent screenings and ongoing monitoring packages available to alert clients to new adverse events post‑hire or post‑engagement. Additionally, we offer consultation on screening policies, tailored consent forms, adverse‑action workflows, and integration support for applicant‑tracking systems or compliance platforms to help clients implement defensible, efficient background‑screening programs.
Digital & Computer Forensics / E-Discovery
Electronic Discovery (E-Discovery)
We provide comprehensive forensic preservation and analysis of digital evidence to support litigation, regulatory inquiries, incident response, and corporate investigations. Our services begin with secure evidence handling and forensically sound device imaging—bit‑for‑bit captures of hard drives, SSDs, mobile devices, removable media, cloud artifacts, and networked storage—performed with write‑blocking, immutable hashing, and documented chain‑of‑custody procedures to preserve evidentiary integrity.
We perform deleted‑data recovery and artifact reconstruction using validated forensic tools and proprietary techniques to recover files, email remnants, slack space items, and partially overwritten content where feasible. Our specialists analyze system and application logs, event timelines, registry and file‑system artifacts, metadata, browser histories, chat and messaging remnants, email headers, and cloud service records to reconstruct user activity, data flows, and timelines pertinent to the matter.
Network and server forensics include packet capture analysis, firewall and proxy log review, authentication and access logs, and correlation of telemetry to identify lateral movement, data exfiltration, or unauthorized access. We also support mobile forensics—acquiring device backups, app data, geolocation artifacts, and secure messaging content—while complying with legal and technical constraints for various platforms.
Our forensic analysts produce court‑admissible, technically detailed reports that document acquisition methods, toolsets and versions, validation checks, timelines of action, evidence correlations, and interpretive findings presented in clear, non‑technical language for legal teams and decision makers. Reports include evidentiary exhibits, annotated file inventories, hash lists, reconstructed timelines, and recommended preservation and remediation steps.
We provide targeted e‑discovery support and evidence staging services to streamline legal workflows: tailored data culling, forensic export and conversion to reviewable formats, tagging and privilege flags, TAR and predictive coding coordination, metadata preservation for production, and secure document repositories for review. Our team integrates with counsel to define scope, sampling strategies, and defensible preservation orders, and we can prepare production‑ready bundles conforming to court rules or vendor specifications.
Additional services include malware and threat‑actor attribution analysis, reverse engineering of suspicious binaries, recovery of encrypted containers when lawful access is granted, and expert witness preparation and testimony. We maintain secure handling of evidence with encrypted storage, role‑based access controls, and auditable logs to protect chain of custody and client confidentiality.
All work is conducted under applicable legal frameworks and standards, with alignment to industry best practices, documented methodologies, and peer‑reviewable processes. We coordinate with outside counsel, incident‑response teams, regulatory contacts, and law enforcement when required, ensuring that preservation and analysis activities support investigative goals, regulatory compliance, and courtroom admissibility.


AI-Enhanced Forensic Image Analysis
Our team specializes in AI‑enhanced forensic image analysis, delivering precise, high‑quality investigative visuals and expert interpretation to support legal, corporate, insurance, and security‑focused matters. We combine advanced machine‑learning techniques, computer vision, and traditional forensic methodologies to authenticate, clarify, and examine digital imagery from cameras, smartphones, CCTV, drones, and social‑media sources, producing results that are both technically robust and legally defensible.
Services include image authentication to detect manipulation or tampering through metadata analysis, error level analysis, compression and file‑structure inspection, and AI‑assisted anomaly detection; enhancement and clarification to recover detail from low‑resolution, low‑light, or motion‑blurred frames using supervised deblurring, super‑resolution, and noise‑reduction models; and frame‑by‑frame analysis to extract timelines, object and facial recognition cross‑referencing, gait and behavioral assessments, and vehicle or item identification. We also perform photogrammetric measurements, perspective correction, and geolocation attribution using visual landmarks, shadow analysis, and corroborating metadata.
Every case follows strict evidence‑handling protocols: documented chain‑of‑custody, secure ingestion and storage of original files, immutable hashing of source media, and detailed methodological reporting that discloses tools, parameters, and validation steps. Deliverables include annotated, court‑ready image packages, comparison plates, annotated timelines, technical affidavits, expert reports, and when required, qualified witness testimony explaining methods and findings in plain language for judicial or administrative use.
Our analysts balance automated AI outputs with human expert review to mitigate algorithmic bias and ensure interpretive reliability, and we validate models against known controls and industry benchmarks. We maintain strict confidentiality, encrypted data handling, and access controls to protect sensitive material and client privacy. When analyses implicate privacy or legal constraints, we coordinate with counsel to secure necessary authorizations and to align reporting with evidentiary standards.
By integrating state‑of‑the‑art AI tools with rigorous forensic practice and clear documentation, we provide actionable visual evidence that strengthens investigative narratives, supports dispute resolution, and enhances situational understanding for decision makers.
Social Media Search
We conduct comprehensive social‑media investigations to gather, preserve, and analyze public and otherwise accessible social accounts and content in a forensically sound, legally defensible manner. Our investigators collect posts, images, videos, comments, profile metadata, follower lists, and interaction histories across major platforms and niche networks, preserving original timestamps, contextual threads, and supporting artifacts to maintain evidentiary integrity.
We validate account ownership and identities by correlating usernames, email and phone indicators, cross‑platform aliases, device‑specific posting patterns, and corroborating public records or known personal details. Timeline reconstruction links sequential posts, edits, and deletions to build clear event chronologies, while geolocation cues—geo‑tags, embedded metadata, check‑ins, image shadows and landmarks, and corroborating location data from other sources—are analyzed to substantiate whereabouts and movement.
Network analysis maps relationships, interaction patterns, and influence pathways to identify associates, co‑conspirators, or corroborating witnesses. We apply OSINT techniques and proprietary search tools to uncover archived or deleted content, alternate accounts, private‑to‑public transition points, and content propagation across groups, pages, and external websites. Our process includes preservation steps such as authenticated screenshots, native file exports, platform‑specific download formats, and documented chain‑of‑custody to support admissibility.
Analytical deliverables include annotated reports, source‑referenced exhibits, indexed multimedia packages, graphical timelines, and social graphs that contextualize findings for litigation, background investigations, compliance reviews, or behavioral corroboration. We provide credibility assessments, content provenance notes, and methodology disclosures so that results withstand scrutiny in discovery and court proceedings.
All investigations respect applicable privacy laws, platform terms of service, and evidentiary rules. When required, we coordinate with counsel to obtain proper legal process for restricted or private data, and we document authorizations and search parameters. Communications and data handling are secured through encrypted channels and access controls to protect sensitive client matters.
Private & Family Law Investigations

Domestic Surveillance Investigations
We offer comprehensive surveillance solutions for civil, corporate, and personal cases, providing adaptable coverage that fits the timeframe, complexity, and risk profile of each matter. Our teams deploy for short‑term assignments such as targeted checks or single‑event monitoring, as well as long‑term engagements that require pattern analysis, habitual movement documentation, or ongoing asset and personnel observation.
Our operatives are vetted, professionally trained, and skilled in covert techniques that prioritize safety, legality, and minimized visibility. We use industry‑standard methods and best practices for planning operations—advance reconnaissance, risk assessments, route and venue analyses, and contingency planning—to maximize effectiveness while reducing exposure for field personnel and subjects.
We employ high‑resolution photographic and video recording equipment, long‑range optics, low‑light and infrared systems, discrete audio capture where lawful, and GPS or telematics integration when authorized and appropriate. Footage is captured with time‑stamped metadata and geolocation references when possible to support authenticity. Field teams combine mobile and fixed surveillance posts, aerial observation where permitted, and vehicle or pedestrian tracking tactics tailored to the investigative objective.
Meticulous reporting accompanies every operation: contemporaneous field logs, annotated timelines, corroborative stills and clip packages, witness summaries, and analytical narratives that contextualize observed behavior. All materials are handled under strict chain‑of‑custody procedures, securely stored with access controls, and delivered in court‑ready formats suitable for litigation, regulatory inquiries, or internal decision‑making. We can include notarized affidavits of observation, authenticated exhibits, and expert summaries on request.
Throughout engagements we comply with applicable federal, state, and local laws, respect privacy boundaries, and consult with retained counsel to ensure methods align with legal strategies and evidentiary needs. Our approach balances discretion, thoroughness, and defensibility, providing clients with reliable intelligence, clear documentation, and strategic recommendations based on observed activity and verified trends.
Infidelity / Cheating Investigations
We conduct discreet, lawful investigations to verify suspected marital infidelity, providing clients with clear, actionable intelligence while maintaining the highest standards of professionalism and confidentiality. Our services employ vetted surveillance teams who are trained in covert observation techniques, photographic and video documentation, and evidence preservation to corroborate findings. We combine real‑time field reporting, time‑stamped multimedia capture, and behavioral analysis to construct an accurate, defensible timeline of events that reflects movements, meetings, and interactions relevant to the inquiry.
All operations are planned with attention to legal constraints and privacy considerations, and we conduct our investigations in strict compliance with Michigan law and applicable court rules. Before initiating field work we consult with clients and, where appropriate, with retained counsel to define objectives, permissible methods, and evidentiary needs. Our protocols emphasize minimizing intrusion while maximizing verifiable documentation: advance reconnaissance, route and venue assessments, risk mitigation for field teams, and contemporaneous logs to support admissibility.
We also perform supplementary research—social‑media monitoring, digital footprint reviews, public record checks, and liaison with local contacts—to corroborate surveillance findings and identify patterns of behavior. Reports include annotated timelines, authenticated multimedia exhibits, witness summaries, and credibility assessments that anticipate evidentiary scrutiny in family‑court or related proceedings. We maintain secure chain‑of‑custody practices for all recordings and materials and offer options for notarized affidavits, expert affidavits, or in‑court testimony if required.
Throughout every engagement we uphold strict confidentiality, provide discrete client communications, and offer guidance on legal and privacy implications of the findings. Our goal is to deliver reliable, court‑ready evidence to support informed decisions in personal and legal contexts while ensuring all investigative work remains lawful, ethical, and professionally documented.


Child Custody / Divorce Investigations
We provide sensitive, court‑ready investigative support specifically tailored for family law matters, delivering reliable, discreet, and legally defensible intelligence to inform custody, visitation, and related proceedings. Our services are designed to document living arrangements, parental conduct, and child welfare while prioritizing the safety, privacy, and best interests of children and all parties involved.
Core services include custody verification and cohabitation checks to confirm actual residence, household composition, and overnight patterns; child welfare monitoring to observe caregiving quality, supervision practices, attendance at school or medical appointments, and any indicators of neglect or endangerment; and targeted documentation for hearings such as time‑stamped photographs, video recordings when permissible, contemporaneous investigator notes, and detailed activity logs. We craft reports and exhibits to meet evidentiary standards and to be admissible in family court, with careful attention to chain‑of‑custody, authentication, and jurisdictional rules.
Additional offerings include supervised exchange monitoring, background and suitability checks of new partners or caregivers, verification of employment and travel histories, social‑media and digital footprint reviews for relevant behavior, and corroborative witness interviews. When appropriate and lawful, we perform GPS‑assisted movement analysis, location verification, and pattern mapping to substantiate claims about routines, travel, or residence changes.
All investigative activity is conducted with strict compliance with local laws, court orders, and privacy protections. We coordinate with retained counsel to align scope and methods to legal strategy, obtain necessary permissions or court approvals for recordings or intrusive measures, and provide pre‑trial briefing materials. Our investigators are trained to interact respectfully with children and vulnerable adults, to minimize trauma or disruption, and to preserve evidentiary value without compromising family stability.
Deliverables are practical and courtroom focused: concise, well‑organized, litigation‑ready reports; authenticated multimedia exhibits; witness statements and credibility assessments; recommended next steps for presenting evidence; and, when needed, expert testimony or affidavit preparation. Throughout engagements we maintain strict confidentiality, secure evidence handling, and transparent status updates to support clients and counsel in achieving child‑centered, legally sound outcomes.
Elder Abuse Investigations
We investigate reports of physical, financial, or emotional abuse of vulnerable adults with sensitivity, professionalism, and strict adherence to legal and ethical standards. Our multidisciplinary approach combines covert welfare checks, targeted interviews, comprehensive financial-transaction reviews, and thorough caregiver background checks to identify signs of mistreatment, exploitation, neglect, or undue influence.
Our covert welfare checks and on-site verifications are conducted by trained investigators who assess physical safety, living conditions, medication management, and immediate risk indicators while minimizing distress to the subject. We document observations with time-stamped notes, photographs or video when lawful and appropriate, and maintain careful chain-of-custody procedures for any collected evidence.
Financial reviews examine bank records, transaction histories, beneficiary changes, unusual withdrawals, transfers to third parties, and patterns consistent with financial exploitation. We work with forensic accountants and financial institutions when necessary to trace asset movement, identify unauthorized transactions, and build a clear, evidentiary financial timeline.
Caregiver and household vetting includes criminal-history checks, employment verifications, reference interviews, licensing and certification confirmation, and social-media screening to detect red flags or unexplained relationships. Investigations may also incorporate witness interviews, medical‑record coordination (with appropriate releases), and targeted surveillance when required to corroborate allegations and document interactions.
We collaborate closely with adult protective services, healthcare providers, law enforcement, and retained counsel to ensure investigations progress within statutory frameworks and to facilitate protective interventions, emergency remediations, or civil and criminal remedies. Throughout each case we prioritize the subject’s dignity and safety, provide welfare and safety recommendations, and offer detailed, litigation-ready reports that include evidentiary documentation, timelines, risk assessments, and recommended next steps for guardianship, restraining orders, asset protection, or prosecution.
All operations comply with applicable privacy laws and reporting obligations; we maintain secure handling of sensitive information, clear chain-of-custody records, and transparent communication with authorized parties to support safeguarding the vulnerable adult and achieving appropriate legal and social outcomes.


Missing Persons Investigation
Our comprehensive services integrate advanced skip tracing, targeted field inquiries, social‑media and OSINT searches, and liaison with law enforcement or local authorities when appropriate to locate and verify subjects. We combine multiple investigative disciplines—database research, public‑record analysis, digital footprint mapping, financial and address history correlation, and on‑the‑ground verification—to develop reliable, corroborated leads and reduce false positives.
Our process begins with intake and case scoping to define lawful objectives, permissible data sources, and verification thresholds. We then perform layered research using proprietary databases, government and court records, social‑platform analytics, geolocation artifacts, and other open and commercial feeds. Where necessary, we deploy field investigators to conduct interviews, doorstep checks, surveillance, or site inspections to confirm presence, identity, and circumstances.
When investigations intersect with criminal activity or public‑safety concerns, we coordinate with relevant law‑enforcement agencies and follow protocols to preserve evidence and ensure proper chain of custody. Throughout every engagement we prioritize compliance with applicable laws, privacy regulations, and ethical standards, documenting sources, methods, and consent where required to preserve admissibility and defensibility.
Deliverables include verified contact details, location reports, movement timelines, source‑mapped documentation, risk and welfare assessments, and recommended next steps tailored to client needs—whether for service of process, recovery actions, witness procurement, or case development. We maintain secure data handling, encrypted communications, and strict confidentiality at every phase, and we provide transparent status updates and documented case files to support legal or operational follow‑through.
Legal Support Services
Process Service / Process Serving
We provide reliable process-serving services across jurisdictions through our vetted network of local partners and field agents, ensuring timely and compliant delivery of legal documents. Our teams handle routine and complex service tasks, coordinate cross‑jurisdictional filings, and maintain chain‑of‑custody documentation to support judicial requirements and case records.
Each service includes preparation and execution of notarized affidavits of service, photographic or video evidence when permissible, and detailed status tracking with time‑stamped notifications and delivery confirmations. We document attempts, refusals, and any nonservice reasons, and provide follow‑up actions such as reattempt scheduling or alternative service strategies tailored to the matter and court rules.
For complex, evasive, or high‑risk subjects, we coordinate advanced skip‑tracing, surveillance, and field verification to locate individuals and enable successful service. Our protocols emphasize legal compliance, personal safety of our field personnel, and respect for privacy and local statutes. We also offer expert consultation on substituted service, constructive service, and other permitted methods, and we work closely with counsel to ensure methods align with procedural requirements.
Deliverables include completed affidavits and proofs of service formatted for immediate filing, supporting multimedia evidence, case logs, and recommended next steps for unresolved attempts. Our cross‑jurisdictional capabilities, quality control measures, and documented chain‑of‑custody practices give clients confidence that service will be executed professionally, defensibly, and in accordance with applicable laws and court procedures.


Skip Tracing
Our advanced skip-tracing services locate hard-to-find individuals, including debtors, witnesses, defendants, and missing persons, by combining proven investigative methods with modern data tools. We leverage proprietary databases, comprehensive public-record searches, open-source intelligence (OSINT), social-media analysis, telecommunications and address-history data, and commercial data feeds to create robust leads and corroborate identities.
Our process includes research and data aggregation, pattern analysis of financial and contact records, link-charting of associates and known addresses, and predictive analytics where appropriate to identify likely locations. We complement desk-based investigation with field verification, covert or overt surveillance as required, doorstep inquiries, and coordination with local contacts or authorities to confirm whereabouts and deliver actionable intelligence.
We adhere to all applicable laws and regulatory guidelines governing privacy, data usage, and investigator conduct, and we document sources, search methodologies, and verification steps to ensure defensibility of results. Deliverables include verified contact information, location reports, movement timelines, risk and safety assessments for planned engagements, and recommendations for lawful next steps such as service of process or coordinated retrieval. Our approach is efficient, discreet, and tailored to the urgency and sensitivity of each case, with secure handling of data and clear communication throughout the investigation.
Witness Interviews
We conduct professional, law‑compliant witness interviews and systematic statement collection to support investigations, dispute resolution, and litigation. Our investigators are trained in evidence‑preserving interview techniques—establishing rapport, avoiding leading questions, and documenting testimony in a clear, consistent manner—to protect witness credibility and legal admissibility. Interviews are carried out in accordance with applicable laws and jurisdictional rules, with attention to consent, privacy, and the protection of vulnerable witnesses.
Our services include pre‑interview case preparation, development of tailored question frameworks, and scene or context review to ensure interviews are focused and relevant. We use a mix of in‑person interviews, recorded telephonic interviews, and secure video testimony sessions as appropriate, always obtaining required permissions and providing contemporaneous notices when recording. Statements are captured in written, audio, and/or video formats based on legal needs and client preference, and are transcribed, time‑stamped, and authenticated to create defensible records.
We also provide witness management services: coordinating logistics, arranging secure locations, preparing witnesses for depositions or court appearances, and advising on witness support measures. Chain‑of‑custody and evidence integrity protocols are strictly followed for all recordings, documents, and exhibits, and we maintain detailed interview logs, consent forms, and confidentiality agreements. Each engagement concludes with professionally prepared, litigation‑ready statements, witness summaries, credibility assessments, and recommended next steps to strengthen case strategy and preserve evidentiary value.


Asset Research and Recovery Investigations
We locate hidden or concealed assets, uncover beneficial ownership structures, and identify offshore holdings to support judgments, collections, or settlement negotiations. Our investigative teams combine traditional intelligence techniques with modern digital-forensic methods to trace asset flows, map ownership networks, and locate real property, bank accounts, investment vehicles, corporate interests, and privately held valuables that may be obscured by nominees, shell entities, or complex trust arrangements.
We coordinate closely with retained counsel, forensic accounting specialists, and, when appropriate, law enforcement or regulatory partners to develop legal and enforcement strategies tailored to each matter. Our services include comprehensive asset tracing, document and public-record searches, corporate and beneficial-ownership due diligence, bank and transactional analysis, undercover asset verification, and on-the-ground surveillance to confirm the existence and location of high-value items.
We prepare litigation-ready asset reports that include evidentiary documentation, chain-of-custody records, financial timelines, ownership charts, and recommended enforcement actions such as writs, garnishments, subpoenas, or international mutual legal assistance requests. Our approach prioritizes compliance with applicable laws and cross-border legal protocols, escrowed handling of sensitive information, and secure coordination with financial investigators, forensic accountants, and private counsel to maximize recoveries and support effective resolution of outstanding claims.
GPS Tracking
When lawful and properly authorized, GPS tracking provides valuable location intelligence to support investigative objectives and case development. Our teams employ court-compliant protocols for deployment, evidence collection, and chain-of-custody preservation, ensuring that all tracking activity meets applicable statutory requirements, court orders, and evidentiary standards. We coordinate closely with retained counsel and, when necessary, with issuing authorities to verify legal authority before initiating tracking, and we document authorizations and operational details to support admissibility.
Our GPS services include device selection and configuration, secure installation and removal, encrypted data capture, and robust storage practices that maintain integrity and confidentiality. Collected location data is analyzed using industry-standard tools to produce clear, court-ready reports, timelines, and geo-visualizations that illuminate movement patterns, proximity events, and corroborating timelines for investigative or litigation needs.
We maintain strict policies for access control, data retention, and secure transfer of information to clients and legal teams, and we dispose of or archive tracking data in accordance with legal requirements and client instructions. All operations are conducted within the bounds of the law, with a priority on protecting privacy rights, minimizing unnecessary intrusion, and ensuring that tracking evidence can withstand legal and judicial scrutiny.


Notary Public Services
We provide on-site and in-office notary services to support a wide range of legal, investigative, and administrative needs. Our notaries are commissioned and experienced in executing affidavits, service documents, investigative paperwork, powers of attorney, and other sworn or notarized instruments. We offer standard notarization services, witness attestations, certified true copies, acknowledgments, jurats, and oaths or affirmations as required by the document and jurisdiction.
Our mobile notary option brings certified notary services directly to residences, offices, hospitals, or event locations for client convenience and continuity of operations. We can coordinate appointments, verify identities, ensure proper document execution, and provide chain-of-custody documentation when needed to support evidentiary or legal processes. For corporate clients and investigative teams, we also support batch notarizations, notarized affidavits for service of process, and secure handling of sensitive documents, including secure delivery and recordkeeping.
All notarizations are performed in accordance with applicable state laws and professional standards, with careful attention to signer competency, proper identification, and completed seals and endorsements to ensure legal validity. We maintain strict confidentiality, detailed transaction logs, and can provide certified copies or apostille services when international use is required, helping to streamline legal workflows and reduce delays.
